文章目录
-
- 一、生成相关证书
- 二、配置elasticSearh
- 三、配置kibana
- 四、配置logstash
- 五、配置filebeat
- 六、连接https es的java api
一、生成相关证书
ps:主节点操作
-
切换用户:su es
-
进入目录:cd /home/es/elasticsearch-7.6.2
-
创建文件:vi instances.yml
instances: - name: "master" ip: - "192.168.248.10" - name: "slave1" ip: - "192.168.248.11" - name: "slave2" ip: - "192.168.248.12" - name: "kibana" ip: - "192.168.248.10" - name: "logstash" ip: - "192.168.248.10" - name: "filebeat" ip: - "192.168.248.10" -
生成证书:/home/es/elasticsearch-7.6.2/bin/elasticsearch-certutil cert ca –pem –in instances.yml –out certs.zip
-
解压得到各个证书:unzip certs.zip
二、配置elasticSearh
ps:三个节点
-
切换用户:su es
-
将解压得到的三个文件夹文件拷贝到各个节点的/home/es/elasticsearch-7.6.2/config下,如master节点:ca.crt、master.crt、master.key
-
三个节点配置,末尾添加配置:vi /home/es/elasticsearch-7.6.2/config/elasticsearch.yml
ps1:根据名字配置master和slave1和slave2
ps2:如果之前配置过密码,需要将密码的配置先移除xpack.security.http.ssl.enabled: true xpack.security.http.ssl.key: master.key xpack.security.http.ssl.certificate: master.crt xpack.security.http.ssl.certificate_authorities: ca.crt xpack.security.enabled: true xpack.security.transport.ssl.enabled: true xpack.security.transport.ssl.key: master.key xpack.security.transport.ssl.certificate: master.crt xpack.security.transport.ssl.certificate_authorities: ["ca.crt"] -
如果是用root用户拷贝的,记得赋权:chown -R es:es /home/es
-
启动
cd /home/es/elasticsearch-7.6.2/bin nohup /home/es/elasticsearch-7.6.2/bin/elasticsearch & -
设置密码:/home/es/elasticsearch-7.6.2/bin/elasticsearch-setup-passwords interactive
ps1:可以统一设置一个密码ffcsict123
ps2:如果已经设置过密码了,可以忽略。或者也可以删除es的 .security-7 索引,重新执行设置密码的操作也可以
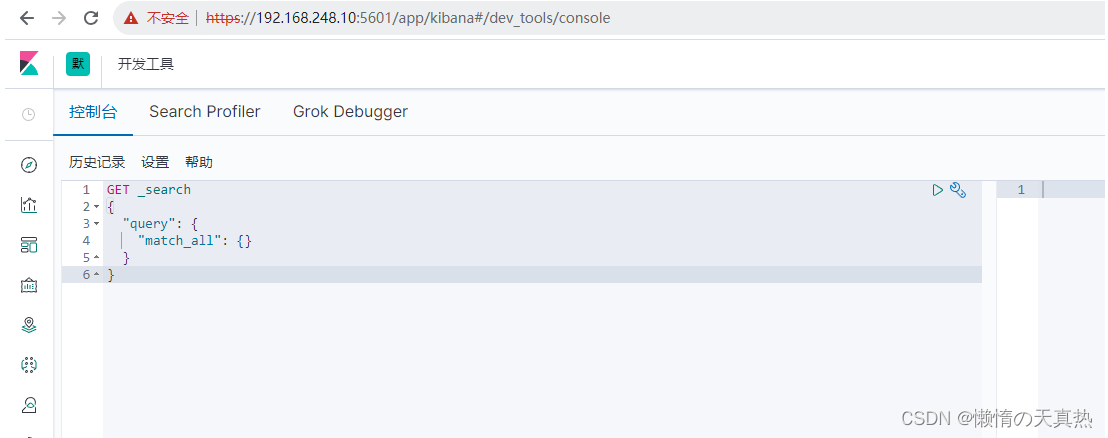
三、配置kibana
-
将kibana证书放到/home/es/kibana-7.6.2-linux-x86_64/config下:kibana.crt、ca.crt、kibana.key
-
配置:vi /home/es/kibana-7.6.2-linux-x86_64/config/kibana.yml
# 修改 elasticsearch.hosts: ["https://192.168.248.10:9200","https://192.168.248.11:9200","https://192.168.248.12:9200"] # 末尾添加 # 这三个路径写成相对路径会被错,写绝对路径才行,不知道为啥 server.ssl.enabled: true server.ssl.certificate: /home/es/kibana-7.6.2-linux-x86_64/config/kibana.crt server.ssl.key: /home/es/kibana-7.6.2-linux-x86_64/config/kibana.key elasticsearch.ssl.certificateAuthorities: ["/home/es/kibana-7.6.2-linux-x86_64/config/ca.crt"] elasticsearch.username: "kibana" elasticsearch.password: "ffcsict123" -
如果是用root用户拷贝的,记得赋权:chown -R es:es /home/es
-
启动:nohup /home/es/kibana-7.6.2-linux-x86_64/bin/kibana &
-
访问:https://192.168.248.10:5601
四、配置logstash
-
将logstash证书放到/home/es/logstash-7.6.2/config下:logstash.crt、ca.crt、logstash.key
-
修改配置文件:vi /home/es/logstash-7.6.2/config/logstash.yml
xpack.monitoring.enabled: true xpack.monitoring.elasticsearch.username: logstash_system xpack.monitoring.elasticsearch.password: ffcsict123 xpack.monitoring.elasticsearch.hosts: ["https://192.168.248.10:9200"] xpack.monitoring.elasticsearch.ssl.certificate_authority: "/home/es/logstash-7.6.2/config/ca.crt" -
修改配置文件:vi /home/es/logstash-7.6.2/config/logstash-sample.conf
output { elasticsearch { hosts => ["https://19服务器托管网2.168.248.10:9200","https://192.168.248.11:9200","https://192.168.248.12:9200"] index => "testlog-%{+YYYY.MM.dd}" user => "elastic" password => "ffcsict123" ssl => true cacert => "/home/es/logstash-7.6.2/config/ca.crt" } } -
启动:nohup /home/es/logstash-7.6.2/bin/logstash -f /home/es/logstash-7.6.2/config/logstash-sample.conf &
五、配置filebeat
——————–如果logstash不需要转https,则可以忽略以下步骤—————–
-
杀死logstash进程
-
将 logstash.key 转换为 PKCS#8 格式
cd /home/es/logstash-7.6.2/config openssl pkcs8 -in logstash.key -topk8 -nocrypt -out logstash.pkcs8.key -
由于我们一个logstash服务,会有很多filebeat服务写日志进来。如果将logstash改为https访问,需要将所有涉及的filebeat都进行改配置。所以如果只是要求es改造为https,可以不改造logstash。如果需要改造,则修改配置文件:vi /home/es/logstash-7.6.2/config/logstash-sample.conf
input { beats { port => 5044 ssl => true ssl_certificate_authorities => ["/home/es/logstash-7.6.2/config/ca.crt"] ssl_certificate => "/home/es/logstash-7.6.2/config/logstash.crt" ssl_key => "/home/es/logstash-7.6.2/config/logstash.pkcs8.key" ssl_verify_mode => "force_peer" } } -
启动logstash:nohup /home/es/logstash-7.6.2/bin/logstash -f /home/es/logstash-7.6.2/config/logstash-sample.conf &
-
将filebeat证书放到/home/es/filebeat-7.6.2-linux-x86_64下:filebeat.crt、filebeat.crt、filebeat.key
-
配置filebeat:vi /home/es/filebeat-7.6.2-linux-x86_64/filebeat.yml
output.logstash: hosts: ["192.168.248.10:5044"] ssl.certificate_authorities: ["/home/es/filebeat-7.6.2-linux-x86_64/ca.crt"] ssl.certificate: "/home/es/filebeat-7.6.2-linux-x86_64/filebeat.crt" ssl.key: "/home/es/filebeat-7.6.2-linux-x86_64/filebeat.key" -
启动:nohup /home/es/filebeat-7.6.2-linux-x86_64/filebeat -e -c /home/es/filebeat-7.6.2-linux-x86_64/filebeat.yml &
六、连接https es的java api
import org.apache.http.HttpHost;
import org.apache.http.auth.AuthScope;
import org.apache.http.auth.UsernamePasswordCredentials;
import org.apache.http.client.CredentialsProvider;
import org.apache.http.client.config.RequestConfig;
import org.apache.http.conn.ssl.NoopHostnameVerifier;
import org.apache.http.impl.client.BasicCredentialsProvider;
import org.apache.http.impl.nio.client.HttpAsyncClientBuilder;
import org.apache.http.ssl.SSLContextBuilder;
import org.apache.http.ssl.SSLContexts;
import org.elasticsearch.action.admin.indices.alias.get.GetAliasesRequest;
import org.elasticsearch.client.*;
import org.elasticsearch.cluster.metadata.AliasMetadata;
import org.springframework.core.io.ClassPathResource;
import javax.net.ssl.SSLContext;
import java.io.IOException;
import java.io.InputStream;
import java.security.KeyStore;
import java.security.cert.Certificate;
import java.security.cert.CertificateFactory;
import java.util.*;
/**
* @author 天真热
* @create 2023-09-02 20:25
* @desc
**/
public class elkDemo {
public static String ip = "192.168.248.10";
public static String port = "9200";
public static String esUsername = "elastic";
public static String esPassword = "ffcsict123";
public static void main(String[] args) throws IOException {
{
RestHighLevelClient clinet = getConnection();
ListMapString, Object>> indexs = getIndex(clinet);
System.out.println(indexs);
}
}
/**
* 创建链接
* @return
*/
public static RestHighLevelClient getConnection() {
// 创建凭据提供程序
final CredentialsProvider credentialsProvider = new BasicCredentialsProvider();
credentialsProvider.setCredentials(AuthScope.ANY, new UsernamePasswordCredentials(esUsername, esPassword));
RestClientBuilder http = RestClient.builder(new HttpHost(ip, Integer.parseInt(port), "https"))
.setRequestConfigCallback(new RestClientBuilder.RequestConfigCallback() {
@Override
public RequestConfig.Builder customizeRequestConfig(RequestConfig.Builder requestConfigBuilder) {
requestConfigBuilder.setConnectTimeout(700000);
requestConfigBuilder.setSocketTimeout(600000);
requestConfigBuilder.setConnectionRequestTimeout(100000);
return requestConfigBuilder;
}
}).setHttpClientConfigCallback(new RestClientBuilder.HttpClientConfigCallback() {
@Override
public HttpAsyncClientBuilder customizeHttpClient(HttpAsyncClientBuilder httpAsyncClientBuilder) {
return httpAsyncClientBuilder.setSSLContext(buildSSLContext())
.setSSLHostnameVerifier(NoopHostnameVerifier.INSTANCE).setDefaultCredentialsProvider(credentialsProvider);
}
});
return new RestHighLevelClient(http);
}
/**
* 获取所有索引
*/
public static ListMapString, Object>> getIndex(RestHighLevelClient esHighInit) throws IOException {
ListMapString, Object>> resultList = new ArrayList();
GetAliasesRequest request = new GetAliasesRequest();
GetAliasesResponse alias = esHighInit.indices().getAlias(request, RequestOptions.DEFAULT);
MapString, SetAliasMetadata>> map = alias.getAliases();
map.forEach((k, v) -> {
if (!k.startsWith(".")) {//忽略elasticesearch 默认的
Map map1 = new HashMap();
map1.put("indexName", k);
resultList.add(map1);
}
});
return resultList;
}
/**
* 创建证书验证
* @return
*/
private static SSLContext buildSSLContext() {
ClassPathResource resource = new ClassPathResource("master.crt");
SSLContext sslContext = null;
try {
CertificateFactory factory = CertificateFactory.getInstance("X.509");
Certificate trustedCa;
try (InputStream is = resource.getInputStream()) {
trustedCa = factory.generateCertificate(is);
}
KeyStore trustStore = KeyStore.getInstance("pkcs12");
trustStore.load(null, null);
trustStore.setCertificateEntry("ca", trustedCa);
SSLContextBuilder sslContextBuilder = SSLContexts.custom()服务器托管网
.loadTrustMaterial(trustStore, null);
sslContext = sslContextBuilder.build();
} catch (Exception e) {
e.printStackTrace();
}
return sslContext;
}
}
服务器托管,北京服务器托管,服务器租用 http://www.fwqtg.net
题目:输入1-7数字 输出对应的星期. //输入数字 输出对应的服务器托管网日期! #include int main() { int day = 0; printf(“请输入星期:”); scanf(“%d”, &day); switch (day)…